Knowledge Transfer |
 |
|
|
|
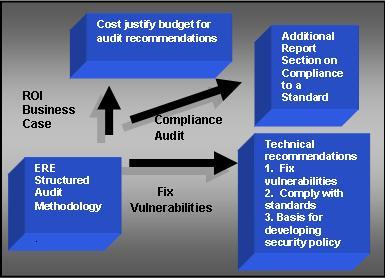
| Audit Methodology |
|
The standardized ERE methodology includes the following elements:
- Offer to sign a bilateral non-disclosure agreement.
- Adherence to the ISO 27001 / 17799 standard for security.
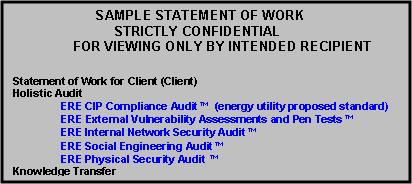
- Provide to a client a detailed statement of work, to clearly create a roadmap for audit activities.
- Provide a fixed price quote with the statement of work, in order to avoid price creep.
- Create a process timeline with the client prior to beginning the audit.
- Utilize a team approach to conduct an audit, with multiple sets of eyes to cross check work product.
- We read all client generated documentation relating to security, privacy and compliance, including the most updated network diagram, policy, end user agreements, training manuals, privacy incident reports, and earlier privacy and security audits.
- Complete external vulnerability assessment prior to commencing on-site audit.
- ERE consultants interview members of a client’s staff representing IT operations, compliance officers if relevant, end users, middle management and senior executives.
- Conduct a “walk-around” of the client’s IT technology room, and offices as required.
- Immediately inform a client during the audit process if we identify any serious problems requiring attention.
- Write and present the audit report.
|
| |
|
|
| Audit Report |
|
The ERE point in time audit report is prepared in a standardized format, which includes:
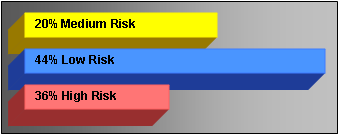
- A non-technical executive summary in which security and compliance problems are described in terms of risk and dollars, with a graphical summary of risk according to threat level.
- A pro-forma business case, accompanied by an executive straw pole, to cost justify the audit report recommendations.
- A technically detailed main body of the report details for each security vulnerability and compliance violation:
- A description of each problem.
- Evidence of the problem.
- A precise recommendation of how to fix each problem.
- A detailed summary technical task list, in a spread-sheet, which identifies:
- Each security problem and compliance violation with a clear technical recommendation to fix each problem.
- The criticality of each problem (high, medium, low), in order for a client to prioritize remedial activities.
- The cross reference with the applicable section reference number of an applicable standard or regulation.
- The cross reference with the applicable section number of the main body of the ERE audit report.
Report Section |
Security vulnerability |
Risk |
Hostname / IP Address / Details |
Business Risks |
Recommended corrective measures |
CIP Non-Compliance Level |
4.5.4 |
Client unable to get access to router interfacing between Corporate network and SCADA network for review, not.... |
Med |
Netopia |
1,2,3,4 |
This router is critical to facilitating communications between the corporate network and the SCADA network and should be fixed or replaced.... |
Level
III |
4.5.4 |
Div A uses the NSA Switch Configuration and Management guidelines to follow when they set up a new switch, however they have not … |
Low |
|
1,2,3 |
Client should utilize the Network Device Build Book (recommended elsewhere) to give them a benchmark to follow.... |
Level
I |
4.5.4 |
The ICCP router is not managed by Client or Div A, unable to review the router configuration. |
High |
|
1,2,3,4,5,6,7 |
Client is unable to audit this device ... a 3rd party is in place and outside of their control, and accept the risk … |
Level
V |
|
|
| |
| |
- A description of the methodology ERE used to conduct the audit.
- Tools for scoring risk over time, as audit report recommendations are implemented.
The goals of the ERE audit report are to provide:
- Clear calls to action to mitigate vulnerabilities and compliance violations.
- Crystal clear audit opinions, using scores and graphs to depict high level results.
- Evidence of problems, such as screen shots, data streams, and photographs.
- A model to assist cost justifying the opinions and recommendations presented in the audit report.
Real Time Monitoring and Reporting
Our audits are available in two forms:
- A point in time gap analysis.
- A 7x24monitoring and real time, perpetual audit service.
Our 7x24 monitoring and perpetual auditing service takes
one point in time compliance auditing into real-time
with real-time trouble ticket reporting on new
vulnerabilities and new compliance violations.
|
|
|
|
|
|
| Consulting for Board Presentation |
|
| |
| |
|
|
|
| Observing Auditor over his Shoulder |
|
| |
| |
|
|
|
| Post Audit Conference |
|
Within two weeks of delivering the audit report, present the findings, answer questions about all elements of the report including:
- Technology and security.
- Our audit methodology and audit tools.
- Risk and ROI.
- Audit opinion and suggestions.
|
| |
|
|
|
| Statement of Work |
|
A comprehensive statement of work, in order to clearly set the client’s expectations, including:
- Details of the audit scope and deliverables.
- Out of scope items.
- The methodology for each step of the audit.
- Time estimated for ERE to complete the audit.
- Client resources required of the client in order for ERE to complete the audit, including personnel, time and resources.
|
| |
|
|
|
|
| Training |
|
Each ERE training session is tuned to meet the specific requirements of each client, according to:
- Area of responsibility of attendees.
- Number of attendees.
- Subject(s) matter.
ERE has several training seminars ready for tuning to meet a client’s specific needs, for:
- NERC CIP compliance.
- How to create a security process within an enterprise.
- Building a security plan and policy.
- Building a compliance plan and policy.
- Privacy policy implementation.
- Implementing response plans.
- Business Continuity Plan.
- Cyber Security Attack.
- Disaster Recovery Plan.
- Response Plans.
|
| |
|
|
|
| |
Contact Us
 |
| |
|
| |
|

