|
Executives who are asked to spend money on
larger information security budgets inevitably
ask for ROI business cases to defend the funding
requests. Although the executive committee
is well versed in the downsides associated with
security breaches, they still need to quantify the
risk, and understand the financial correlation
between risk and cost.
Risk is best conveyed to executives in a numeric format for both:
- Estimating the category of business risks in a business case.
- How well the IT department is progressing with fixing the security vulnerabilities identified in the business case.
Categorizing Security Threats
Security threats are aggressive acts, either
performed in person by hacking or in an automated
fashion by using aggressive technology
agents, which are intended to steal, damage, or
to deny access. Security threats are of course,
directed at specific targets, with specific information
housed on servers and on other network
components.
Threats may be categorized into two broad
categoriesmalicious and non-malicious.
Examples of malicious threats are well publicized
such as viruses, worms, Trojan Horses,
external hacking attacks, and denial of service
attacks. Non-malicious threats are created without
malice or intent, but can result in serious
damage. Examples of non-malicious threats are
improperly patched software, employees using
peer-to-peer file transfer software and instant
messaging, allowing firewall rules to become
outdated and ineffective, and employees allowing
their children to use a corporate laptop to
access the Internet.
Generally non-malicious threats are less serious,
as they can in theory be dealt with by a corporate
security policy and by an IT security policy.
Lack of adherence to policy is the bane of
non-malicious threats. Malicious threats are
generally more serious, as a corporation cannot
elicit cooperation from a party with ill intent.
While a non-malicious threat may have a lifespan
only as long as corporate security policy is
not properly enforced, the lifespan of malicious
threats are ongoing.
The targets of threats are aptly described by
what best practices define as the three pillars of
security. The three pillars of information security
are "confidentiality, integrity, and availability," as
illustrated in Figure 1.
Confidentiality refers to protecting information
from being revealed to unauthorized
parties. Typically associated with ensuring confidentiality
are access controls, user names
and passwords, authentication mechanisms,
protection from hackers including intrusion
detection, protection from malicious code
such as Trojan Horses which could steal data,
viruses / worms which can cause unauthorized
distribution of data, SPAM / phishing,
and social engineering.
Confidentiality is categorized in more security-
oriented organizations such as military, government,
and banks. The more common
classifications are: non-classified, authorized for
classified, secret, and top secret.
Integrity deals with keeping information
accurate and free from unauthorized change.
SarbanesOxley, Ontario Bill 198, HIPAA and
other confidentiality regulations, and NERC
1300 are all strong business drivers for ensuring
data remains untainted. Security issues surrounding
integrity are the same as for confidentiality,
with additional attention paid to regular
monitoring and auditing of data file logs, audit
trails, recovery planning, and enforcing compliance
with security and privacy policy.
Availability deals with the ability to access
data without any obstruction or delay. Many
organizations "live" on their email, ERP, realtime
control (i.e. SCADA) systems, and billing
systems, and cannot afford to have these systems
compromised for any significant time.
Security issues associated with availability
include physical security, disaster recovery planning,
business continuity planning, firewalls and
redundant firewalls, plus all the issues associated
with confidentiality.
Four Quadrants of Security Threats
To calculate risk of a particular security vulnerability,
one must first associate a target with a
threat. For instance, a very serious threat to a
UNIX system which may come in contact with a
Windows target that is not adequately protected
with an updated patch presents a combined risk
level categorized as "low." Risk is
still present, as the insufficiently
patched Windows device may
be susceptible to other threats.
Figure 2 shows the relationship
between threats and risks.
Low risk targets are assets that if
compromised result in little
consequence. Non-malicious
threats have no intent. So a
combination of a low risk vulnerability
with a non-malicious
threat generally falls into the
"green" low risk quadrant.
Similarly high-risk vulnerabilities
associated with malicious
threats are generally found in
the "red" quadrant.

Calculation of Risk
As described in Figure 2, risk
can subjectively categorized as
high, medium, and low. For purposes
of tracking success of
implementing repairs to security vulnerabilities, particularly for large enterprise
audits with multiple regions or locations, risk can also be quantified as a
numerical score. The numeric score is typically calculated using a spreadsheet
shown in Figure 3, instead of the quadrant classification of Figure 2.
| |
|
Error in financial
report resulting
in SOX breach |
Loss of
availability
of billing
system |
Loss of
availability
of SCADA
system |
Loss of
availability of
email service
at head office |
... |
Total |
| |
|
5 |
4 |
5 |
3 |
|
|
| Trojan horse, worm, virus |
5 |
25 |
|
20 |
|
|
|
| External hack attack |
2 |
|
8 |
|
6 |
|
|
| Employee Internet abuse |
4 |
20 |
|
|
12 |
|
|
| Patches on servers not kept current |
4 |
20 |
16 |
20 |
|
|
|
| Firewall not configured correctly |
3 |
|
|
|
9 |
|
|
| ... |
|
|
|
|
|
|
|
| Total |
|
45 |
28 |
40 |
30 |
|
143 |
Figure 3: Score of Risk vs. Targets
As depicted in Figure 3, a numeric value is assigned to each threat and
vulnerability identified in a security audit report. The more dangerous the
threat, the higher its associated value, and similarly for the risk level for
each vulnerability.
In the example of Figure 3, the audit identifies an initial risk score of
143. This figure can then be translated into a percent, where the initial
score is translated into 100%, and as risks are mitigated, the reduced score
can be expressed either as a number or a reduced percent.
Executives who are monitoring the implementation of the audit recommendations
will see the risk score or percent score decrease as the IT staff successfully
implements the recommendations. This exercise provides proof that
value was accrued for the expenditures to implement the recommendations.
Source of Risk Information
The most dependable source of information for assessing actual threats
and risks faced by a corporation is an audit report created by an external,
impartial information security audit firm. The firm should conduct the audit
from a position of least prior knowledge, and should provide in the report:
- A detailed description of all security vulnerabilities, and the threats to which they are susceptible.
- High-level recommendations of how to mitigate each vulnerability.
- A categorization of each vulnerability into a business risk, possibly including a risk score. The risk scores of each vulnerability are totaled for a total audit risk score.
- An executive summary, which explains all of the above in business terms, which executives can understand and upon which they can make decision.
- A pro-forma business case to cost justify all the recommendations of the audit, which is populated with all the key risks, categorized by criticality.
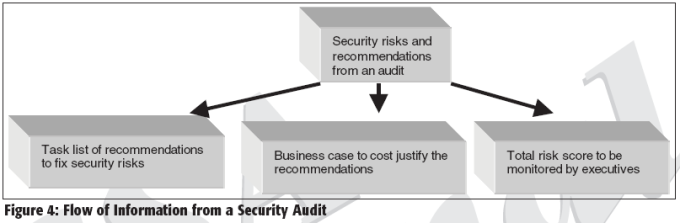
The results of the security audit should be used as input for the following three processes, as illustrated in Figure 4:
- Use the very detailed technical observations of vulnerabilities and recommendations to create a plan to actually fix the problems. The mitigation plan should be implemented within sixty to ninety days of the publication of the audit report.
- Use the pro-forma business case to secure funding to pay the costs to fix the problems, and potentially for a larger security budget.
- Executives can use the diminishing risk score to monitor the progress of the post-audit mitigation plan. Once executives authorize expenditures for mitigating specific risks, they subsequently want to ensure the funds have been well spent. Specifically they want progress reports, on the progress of implementing risk mitigation. Once again, risk is most easily conveyed to executives numerically, or in terms of a score.
Since new risks and threats are always evolving, the overall risk score of
the corporation tends to increase with time, as indicated by the top line in
Figure 5. These new risks and threats arise, principally due to:
- Changes made to the corporate network.
- New Internet threats created since the completion of the last audit.
- Changes in employees and changes in employees' adherence to corporate security policy.
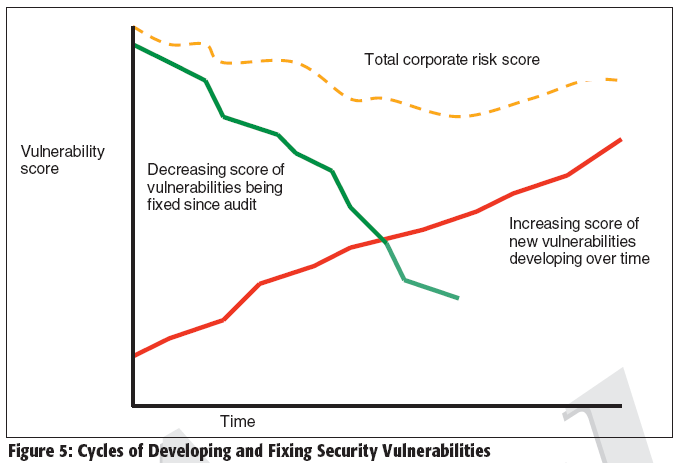
Since new risks may not be uncovered until a new audit is performed,
their risk value and a plan to mitigate them will likewise remain undetermined
until the results of the next audit are published. However, the total
true corporate risk score is in reality a sum of the
(decreasing) score of the known risks plus the
increasing score of the unknown risks.
If risks are expressed as a percent, then the total
corporate risk score cannot be quantitatively evaluated.
In other words, a percent risk score from an
audit report cannot be mixed with an estimated
numeric score for new risks. Therefore, it is incumbent
upon the sponsor of an audit to determine
the score method which will most suit the
intended use of the risk analysis.
Two caveats need to be expressed with regard to this methodology of calculating risk, as follows:
- The third-party auditor should perform an impartial follow-up audit to ensure the recommendations of the previous audit are effectively implemented. This due diligence audit provides assurance to executives that the risk score is accurate and that the vulnerabilities are indeed mitigated.
- Ongoing regular third party audits should be regularly conducted to identify newly developing risks and threats.
Conclusion and Call to Action
Executives can hire experts to identify and quantify the security risks
faced by their organization. Risks can be quantified by a risk score, which
is of most use for a large enterprise audit report. Risks can be expressed
as numeric values or percent of the initial numeric value, depending upon
the intended use of the risk analysis.
The recommendations to mediate the risks can be cost justified by an
ROI based business case. As the IT staff progresses with the mitigation plan
over a two to three month period, executives can monitor the progress by
tracking the diminishing risk score. This quantitative score reduction provides
executives with a method of measuring the accrued value of their
investment in implementing the recommendations.
However, it is prudent to continue the security process with a followup
audit to ensure the recommendations have been implemented
effectively. The follow-up audit provides due diligence for the accuracy
of the reduced score.
Since new risks and threats continue to develop, it is prudent for executives
to advocate ongoing regular security audits to discover and quantify
new risks that threaten their organization.
About the Author
Ron Lepofsky is the President and CEO of ERE Information Security Auditors,
information security and security standards compliance auditors. ERE provides
services to large publicly traded corporations, the financial industry, electrical
utilities, and to large law firms (www.ere-security.com).
|

